Course Highlights and Why Ethical Hacking Course in Bangalore at FITA Academy?
Upcoming Batches
- 17-04-2025
- Weekdays
- Thursday (Monday - Friday)
- 19-04-2025
- Weekend
- Saturday (Saturday - Sunday)
- 21-04-2025
- Weekdays
- Monday (Monday - Friday)
- 26-04-2025
- Weekend
- Saturday (Saturday - Sunday)
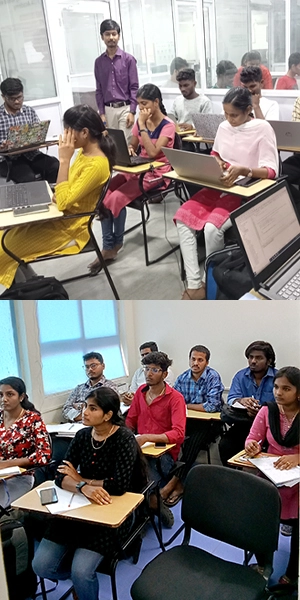
Classroom Training
- Get trained by Industry Experts via Classroom Training at any of the FITA Academy branches near you
- Why Wait? Jump Start your Career by taking the Ethical Hacking Training in Bangalore!
Instructor-Led Live Online Training
- Take-up Instructor-led Live Online Training. Get the Recorded Videos of each session.
- Travelling is a Constraint? Jump Start your Career by taking the Ethical Hacking Online Course!
Ethical Hacking Course Objectives
Ethical Hacking Advanced
- An overview of ethical hacking, distinguishing between hacking and ethical hacking, exploring the scope of learning ethical hacking, and understanding its five phases.
- Learn passive and active reconnaissance techniques, enumeration techniques, and countermeasures.
- Discover network scanning techniques and countermeasures, understand system hacking techniques, and learn more about steganography, steganalysis attacks, and hiding your tracks.
- Learn about installing and configuring virtual machines on Windows and MAC and gain knowledge about installing and using Kali Linux.
- Learn about ZIP and PDF password hacks and learn about Metasploit and how to work with it.
- Use tools like N-map for scanning and advanced commands, understand Burp Suite installation and configuration, and learn about sniffing, malware threats, and analysis.
- Investigate different types of web server attacks.
- Understand techniques and countermeasures for hacking web applications.
- Discover SQL injection attacks and detection tools.
- Understand wireless encryption and cracking methods.
- Learn about IDS, IPS, firewalls, honeypots, and evasion techniques.
- Explore various cloud computing concepts and threats.
- Understand different types of ciphers and attacks.
- Learn about social engineering techniques, advanced techniques, and countermeasures.
- Apply all these techniques in the real-time projects integrated into our Ethical Hacking Course in Bangalore.
Ethical Hacking Expert
- Define penetration testing and understand the roadmap for penetration testing.
- Consider different types of penetration testing and security auditing.
- Understand the importance of establishing your own laboratory.
- Identify hardware and software requirements.
- Learn about using advanced search techniques and OSINT.
- Explore tools like Shodan, FOCA, Maltego, and social engineering toolkits.
- Install and configure advanced scanning tools.
- Discover techniques and tools for vulnerability scanning.
- Understand abuse terminology and database abuse.
- Learn post-exploitation skills using tools like Metasploit. Learn techniques and tools to crack passwords.
- Getting to know information Security Audits, Technical Audits, and Reports.
- Understand OWASP and explore the top 10 vulnerabilities.
- Practical session on critical vulnerabilities and countermeasures.
Ethical Hacking Course Syllabus
Introduction to Ethical Hacking
- What is Hacking?
- What is Ethical Hacking?
- Difference between Hacking and Ethical Hacking
- Learning Scope of Ethical Hacking
- Five Phases of the Ethical Hacking
Enumeration (Reconnaissance - Active)
- Enumeration Techniques
- Enumeration Countermeasures
FootPrinting (Reconnaissance-Passive)
- Various types of Footprinting
- Countermeasures and Footprinting Tools
Network Scanning
- Network Scanning Technique
- Network Scanning Countermeasures
System Hacking Methodology
- Methodologies of System Hacking
- Steganography
- Covering Tracks
- Steganalysis Attacks
Virtual Machine
- Configuration of VM's in the Windows and MAC
- Installation of VM's and OS
- Installation of Software
Kali Linux
- Installation of Kali Linux
- Working of Kali Linux
- Password Hacking for PDF Files and Zip Files
Metasploit
- Introduction to Metasploit concepts
- Working of Metasploit
- Advanced Techniques and Windows Hacking
Tools
N-map
- Scan using Nmap Tool
- Advanced Techniques and Commands
Burp-Suit
- Introduction
- Configuration
- Installation of burp-suit with browsers
- Working with the burp-suit
Sniffing
- Getting to know about Sniffing
- Packet Sniffing Techniques
- How to defend against Sniffing
Malware Threats
- Various Types of Malware
- Different Types of Trojans
- Trojan Analysis and Countermeasures
Virus and Worms
- What is a Virus?
- How does it work?
- Virus Analysis
- Computer Worms
- Malware
- Analysis Procedure and Countermeasures
DoS and DDoS
- What is a Denial of Services (DoS)
- What is the meaning of Distributed Denial of Services (DDoS)
- Various Types of Attacks
- DoS/DDoS Attack Techniques
- Botnets
- DDoS Attack Tools
- DoS/DDoS Countermeasures
Session Hijacking Techniques
- Session Hijacking Techniques and Countermeasures
Servers Attacks - File Servers and Web Server
- Types of Web server Attacks
- Attack Methodology and the Countermeasures
Hacking Web Applications
- Different Web Application Attacks
- Web Application
- Hacking Methodology and the Countermeasures
SQL Injection Attacks
- SQL Injection Attacks
- Injection Detection Tools
Wireless Networks Attacks
- Understanding of Wireless Encryption
- Knowing Wireless Cracking Methodology
- Wireless Cracking Tools
- Wireless Security Tools
IDS, IPS, Honeypots, and Firewalls
- Firewall
- Intrusion Detection System (IDS)
- Honeypot Evasion Techniques
- Evasion Tools and Countermeasures
Cloud Computing Techniques
- Multiple Cloud Computing Concepts
- Cloud Computing Threats and Attack
- Security Tools and Technique
Cryptography
- Types of Cryptography Ciphers
- Public Key Infrastructure (PKI)
- Cryptography Attacks
- Cryptanalysis Tools
Social Engineering
- Understanding of Social Engineering
- Phishing Emails
- Types of Social Engineering Attacks
- Advanced Techniques
- Countermeasures
Further Learning
Career and Opportunities
ETHICAL HACKING - EXPERT
Introduction
- Introduction
- Penetration Testing
- Types of Penetration Testing
- Knowing about Penetration Testing Roadmap
- Security Audit
Building and Setting Up of the Laboratory
- Why set up your Lab
- Hardware, Software Requirements
- Metasploitable Linux
- OWASP Broken Web Applications
- Windows Systems as Victim
Virtual Machine
- Configuration of the VM's in Mac and Windows
- Installing of VM's and configuring OS
Kali Linux
- Kali Linux Installation
- Working of Kali Linux (GUI)
- Working of Kali Linux (CLI)
- Set Up Kali Linux from the ISO File
Collecting Information
Google HDB
- Google Search
- Using Google Keywords for search and finetuning
- Advanced Search Techniques
OSINT - OSINT (Open Source Intelligent)
- Introduction for Information Gathering
- Using Search Engines to Collect Information
- Search Engine Tools like SiteDigger and SearchDiggity
- Shodan
- Gather Information About People
- Web Archives
- Fingerprinting Organisations with Collected Archives - FOCA
- Fingerprinting Tools: Harvester and Recon-NG
- Maltego - Visual Link Analysis Tool
Social Engineering - Techniques)
- Social Engineering Terminologies
- Malware - Terminologies
- Social Engineering Toolkit (SET) for Phishing
- Sending Fake Emails for Phishing
- Voice Phishing: Vishing
Scanning and Enumeration Using Advanced Tools
- Installation
- Advanced Vulnerability Scanning Techniques
- Preventing Complex Attacks
- Effective use of the Tool to identify Weakness
Tools
- Nessus Tool
- Qualys Tool
- N-Map
- Burp-Suit
- Nikto
- Dirb
Exploitation
- Exploitation Terminologies
- Exploit Databases
- Manual Exploitation
- Exploitation Frameworks
- Metasploit Framework (MSF)
- Introduction of MSF Console
- MSF Console and How to Run the Exploit
- Getting to know Meterpreter
- Obtaining a Meterpreter Session
- Meterpreter Basics
Metasploit Framework for the Penetration Testing
- Working with Metasploit
- Windows Hacking
- Creation of Malicious Executable
- Payload crafting like .exe .apk etc
- MSF Venom
- The veil to Create the Custom Payloads
- FatRat - Configuration and Creating the Custom Malware
- Embedding Malware on PDF Files
- Embedding Malware on Word Documents
- Embedding malware in the Firefox Add-ons
- Empire Project in Action
- Exploiting Java Vulnerabilities
Password Cracking
- Password Hashes of the Windows Systems
- Password Hashes of the Linux Systems
- Classification of the Password Cracking
- Password Cracking Tools in Action: Hydra, Cain, Abel, and John the Ripper.
Post Exploitation
- Persistence: What are they?
- Persistence Module of Meterpreter
- Password Hacking for PDF and ZIP File
- Removing Persistence Backdoor
- Next Generation Persistence
- Meterpreter for the Post-Exploitation with the Extensions: Core, Stdapi, and Mimikatz.
- Post Modules of the Metasploit Framework (MSF)
- Collecting Sensitive Data in the Post-Exploitation Phase
OWASP Top 10 Vulnerability
- Introduction on OWASP
- Latest Vulnerabilities
- Practical session for Critical Vulnerabilities
- Countermeasures
Information Security Audit
- Knowing Information Security Audit
- Technical Audits
- Physical Audits
- Administrative Audits
- Audit Preparation and Planning
- Establishing Audit Objectives
- Auditing Application Security
Audit Reporting
- Reporting
Ethical Hacking Course Trainer Profile
- Trainers for the Ethical Hacking Training in Bangalore are certified experts with decades of experience in the field of Cyber Security and Ethical Hacking.
- Students are trained with real-life projects and case studies. Trainers help students to have maximum practical knowledge of different types of Ethical Hacking and Hackers.
- Trainers broaden the knowledge of the students with industry-relevant skills.
- Regular Assessment of the Students with required individual attention.
- Regular doubt clearing and recap sessions are conducted to help students understand the concepts completely.
- Trainers help the students in Resume Building and hone the interpersonal skills of the students.
Learn at FITA Academy & Get Your
Dream IT Job in 60 Days
like these Successful Students!
Student Success Story of Ethical Hacking Course in Bangalore
Vinay Kumar, a B.tech – IT (final year) student had a passion for cybersecurity. Vinay dreamt of becoming an ethical hacker and making a mark in the world of cybersecurity.
Through a referral from his college mate, he discovered FITA Academy, a renowned training centre for IT professionals in Bangalore. Recognizing the need for specialised knowledge in Ethical Hacking, he enrolled in FITA Academy’s Ethical Hacking Institute in Bangalore.
The course, taught by industry experts, covered both the basics and advanced topics. Vinay attended each session regularly and performed well in all the assessments. He also successfully completed real-time projects under the guidance of our expert trainers. At the end of the course, Vinay underwent placement training at FITA Academy. This training provided him with the confidence and skills needed to face recruitment processes head-on.
With his newfound knowledge and polished interview skills, he eagerly stepped into the world of campus placements. He managed to get offers from Cognizant and NTT Data Global. He accepted the offer from NTT Data for the role of ethical hacker with a pay of Rs 3 LPA.
Features of Ethical Hacking Course in Bangalore at FITA Academy
Real-Time Experts as Trainers
At FITA Academy, you will learn from industry experts eager to share their knowledge with learners. You will also get personally mentored by the Experts.
LIVE Project
Get the opportunity to work on real-time projects that will provide you with deep experience. Showcase your project experience and increase your chances of getting hired!
Certification
FITA Academy offers certification. Also, get ready to clear global certifications. 72% of FITA Academy students appear for global certifications and 100% of them clear it.
Affordable Fees
At FITA Academy, the course fee is not only affordable, but you can also pay it in installments. Quality training at an affordable price is our motto.
Flexibility
At FITA Academy, you get the ultimate flexibility. Classroom or online training? Early morning or late evening? Weekday or weekend? Regular Pace or Fast Track? - Choose whatever suits you best.
Placement Support
Tied-up & signed MOUs with over 3000+ small & medium-sized companies to support you with opportunities to kick-start & advance your career.
Why Learn Ethical Hacking Course in Bangalore at FITA Academy?
Live Capstone Projects
Real time Industry Experts as Trainers
Placement Support till you get your Dream Job offer!
Free Interview Clearing Workshops
Free Resume Preparation & Aptitude Workshops

Ethical Hacking Certification Training in Bangalore
FITA Academy provides a certificate of completion after the completion of the Ethical Hacking Training in Bangalore. Obtaining an Ethical Hacking Certification is an indicator of an individual’s proficiency in utilizing hacking tools and securing databases against harmful threats. Possessing this certification can enhance one’s resume and potentially give them an edge during job interviews. FITA Academy in Bangalore offers comprehensive Ethical Hacking Training, which leads to a professional certification for both students and IT professionals.
Certified Ethical Hacker
The Certified Ethical Hacker (CEH) is one of the top certifications available for ethical hackers. Offered by EC-Council, this certification teaches the latest hacking tools and techniques that are used by ethical hackers. It covers various aspects of network security testing and operating system vulnerabilities, providing a blend of performance-based and multiple-choice questions to enhance IT security knowledge and hands-on experience . FITA Academy’s course for Ethical Hacking in Bangalore helps students in the preparation for the CEH certification exam.
Have Queries? Talk to our Career Counselor for more Guidance on picking the
right Career for you!
Placement Session & Job Opportunities after completing Ethical Hacking Course in Bangalore

As per the recent trends, Ethical Hacking is gaining massive importance amidst the organizations due to its necessity in data security. As the world is getting modernized similarly there are several threats to data storage due to the tremendous evolution in technology. Thus, it is necessary for every company to be able to handle these insecurities with respect to data or else this may lead to a huge loss. FITA Academy ensures its students use the abundant opportunities available in the field of Ethical Hacking Books.
“100% placement assistance and training is provided to students after the completion of the course in FITA Academy’s Ethical Hacking Institute in Bangalore.”
Candidates well trained in Ethical Hacking have additional advantages towards the job offered by various leading companies. Some of the industries, which you can try after the completion of the course include : Hotels, Finance, Retail chains, Government agencies and Service providers.
In addition, government agencies like the military, defense, detective, and forensic also employ Ethical Hackers. With security becoming a major concern in both physical environments and online threats. Thus, being a knowledgeable person in this sector will definitely be a boon in this era.
Common Job Profiles that are offered in an Organization are as follows,
- Ethical Hacker
- Security Analyst
- Penetration Tester
- Forensic Investigator
- Security Investigator
- Data Security Specialist
- Network Security Engineer
- Information Security Analyst
- Certified Ethical Hacker (CEH)
- Information Security Manager
- Computer Forensics Investigator
- Security Consultant (Computing / Information Technology/ Networking)
FITA Academy’s Ethical Hacking Course in Bangalore With Placement greatly helps students get placed in the above mentioned roles.
Remuneration offered
Based on the report submitted by PayScale India below is the average salary package that is offered in an organization for candidates of various levels of experience. The Salary and perks may vary based on the organization’s requirements.
- Ethical Hacker Salary For Freshers is around Rs 4,00,000 per annum.
- Candidates with mid-level experience 5-9 years can earn up to Rs 7,20,000 annually.
- Senior-level candidates with 10-12 years of experience may earn up to Rs 1,132,911 per annum.
Job roles
Ethical Hacker
This is the first and foremost job opportunity after completing ethical hacking training. An ethical hacker looks for vulnerabilities on websites and networks. He also tests the security measures of organisations. Most of the time, he finds flaws in the network’s firewall. However, sometimes, he might find other issues such as SQL injection, Python, cross-site scripting (XSS) etc. Once he identifies the issue, he informs the organisation about it so they can fix it. In addition to this, he also recommends ways to improve the security of the website. That said, FITA Academy trains its students to become successful ethical hackers through its Ethical Hacking Institute in Bangalore.
Security Analyst
A security analyst works with the IT department of an organization. He/she performs different tasks such as analyzing the data collected from the network sensors, checking the logs, identifying the loopholes in the system, testing the antivirus programs, etc. In the current scenario, there are many people who want to pursue a career in the field of ethical hacking.
Penetration Tester
A penetration tester uses various tools and techniques to test the security of a company. For example, he analyzes the application layer protocols. He also checks the server-side programming languages. He tries to identify weaknesses in the web applications. After finding out all these things, he reports back to the client. Sometimes, he might even try to hack the system remotely. With the help of Ethical Hacking Training Institute in Bangalore, students will gain knowledge to obtain a career as a penetration tester. They will also learn how to use the tools that are available to them.
Forensic Investigator
Forensic investigators analyse digital evidence found on computers and mobile devices. They collect data from the hard drive or mobile phone. Then, they use special software to retrieve important information from it. Some of the common examples of digital evidence include email’s, chat conversations, documents, pictures, videos, audio files, etc.
Security Investigator
A security investigator investigates various types of crimes such as hacking, fraud, identity theft, etc.
Data security specialist
Data security specialists protect the databases of organizations. Their main task is to make sure that the database does not contain any type of malicious code. They perform regular scans of the database to identify viruses, spyware, adware, etc. Through the course offered by FITA Academy’s Ethical Hacking Institute in Bangalore, students will know what it takes to be a successful Data Security Specialist.
Network Security Engineer
Network security engineers protect the computer networks of organizations. Their primary responsibility is to ensure that no unauthorized person accesses the sensitive information stored online. They check the firewalls, routers, switches, and wireless networks.
Information Security Manager
An Information security manager ensures that the systems are protected against cyber attacks. He/she monitors the network traffic and makes sure that there are no intrusions.
Computer Forensics Investigator
A computer forensics investigator collects digital evidence from a computer or mobile device. He/she stores this evidence in a secure location until the investigation process is over. Candidates who wish to become Computer Forensics Investigators can join FITA Academy’s Ethical Hacking Training Institute in Bangalore.
Security Consultant
A consultant helps companies to improve their security measures. He/she provides advice on how to keep the systems safe. FITA Academy Ethical Hacking Training in Bangalore is an excellent opportunity for aspiring ethical hackers to learn about cybersecurity, data security and hacking techniques.
Success Story of Ethical Hacking Course in Bangalore
Santhosh
Great place to learn Ethical Hacking Course at FITA Academy and they have the patience to answer every question raised in the classroom. Trainers are knowledgeable and share lots of new terms which are easily understandable. Thank you, FITA Academy, for providing me with the best coaching.
Afra fathima
Very good exposure and satisfied to complete my ethical hacking course at FITA Academy. They ensure that the trainer has world-class industry experience in the Cyber security field. Now I got placed in a reputed company as an Information Security Analyst. I am glad that I choose FITA Academy for this.
Akshitha
I had completed my Hacking course at FITA Academy. The trainers gave the best coaching and have in-depth subject knowledge. All of my sessions are only handled by real-time trainers. I am highly satisfied with the training at FITA Academy. I suggest people FITA Academy for students who are seeking to learn the Ethical hacking Course.
Our Students Work at

Frequently Asked Question (FAQ) about Ethical Hacking Course in Bangalore
- Ethical Hacking Courseware is designed by industry experts with more than 10 years of experience in the Networking field.
- Extensive coverage of course with more than 60+ hours of training in our Ethical Hacking Training in Bangalore.
- More than 1,00,000 students trust FITA Academy.
- Ethical Hacking training in Bangalore fees is designed to be affordable for both students and working professionals.
- Flexible Online Ethical Hacking training in Bangalore and offline course timings for the students and professionals.
- Supports students in resume building and provides Interview Tips.
- Certification and placement assistance provided at the end of the course, including mock interviews and discussion of Ethical Hacking Interview Questions and Answers.
We have tie-ups with over 3,000 small to large-scale companies, and most have openings for Ethical Hacker professionals. Furthermore, an active placement cell assists our students persistently and trains them with mock interviews, group discussions and Interview Tips. We train the students efficiently to equip themselves in a professional environment.
The batch size of the Ethical Hacking Course is optimal for 5-6 members per batch. All the students are provided with maximum individual attention. We provide the maximum laboratory session for the students and train the students with real-time projects Ethical Hacking Tutorial and numerous case studies.
Ethical Hacker Trainers in FITA Academy are subject-matter experts. They have over a decade of experience in Networking and CyberSecurity. Also, they provide Corporate Training.
- Established in 2012 by seasoned IT professionals, FITA Academy provides top-notch IT instruction.
- We have instructed 1,00,000+ learners, including working professionals to date.
There is no requirement for prior experience to pursue a career in Cyber Security. Obtaining a Cyber Security certificate can significantly enhance your career prospects. A degree is beneficial, but so is a certificate.
- Ethical Hacking training in Bangalore for beginners to the field and wish to make their mark in cybersecurity.
- IT professionals with a background in cyber security who want to pivot their careers or enhance their skills in the field.
- Anyone interested in pursuing a career in Cyber Security, including Network Administrator, System Administrator, Security Analyst, Security Engineer, Ethical Hacker, Penetration Tester, etc.
General Q & A about Ethical Hacking Course in Bangalore
What is the qualification for ethical hacking course?
How much does ethical hacking course cost?
Which institute is best for ethical hacking?
How many hours to study for ethical hacking?
How long is a hacking course?
Which language is used for hacking?
Is hacking a good career?
Will hackers be replaced by AI?
Can I become a hacker without a degree?
Is HTML important for hacking?
Do I need coding for hacking?
Which company hires as Ethical Hacker?
- Bank of America
- Boeing
- Citi
- Deloitte
- IBM
- Lenovo
- Verizon
- Walmart
Which skill is best for ethical hacking?
- Linux Skills.
- Programming Skills.
- SQL Skills.
- Hardware Knowledge.
- Knowledge in Reverse Engineering.
- Cryptography.
- Database Skills.
- Problem-solving Skills.
What is the salary of a certified Ethical Hacker at Google?
Which country pays the highest salary to an Ethical Hacker?
Do hackers need math?
What are the 3 types of hackers?
Does hacker have a future?
Which type of hacker is highly paid?
Is CEH free?